As a software developer and technology provider, SmartVault takes security seriously. The SmartVault security strategy is well-defined and implemented enterprise wide.
Use this Trust Center to learn about our security posture and request access to our security documentation.
SmartVault’s Information Security Program is designed to protect the confidentiality, integrity and availability of both GetBusy and customer data, such as:
-
The mission and business-critical systems that customers rely upon for cloud services, technical support and other services;
-
Personal and other sensitive information that GetBusy processes during its business, including customer, partner, supplier and employee data residing in GetBusy’s internal systems and third-party platforms; and
-
SmartVault source code and other sensitive data against theft and malicious alteration.
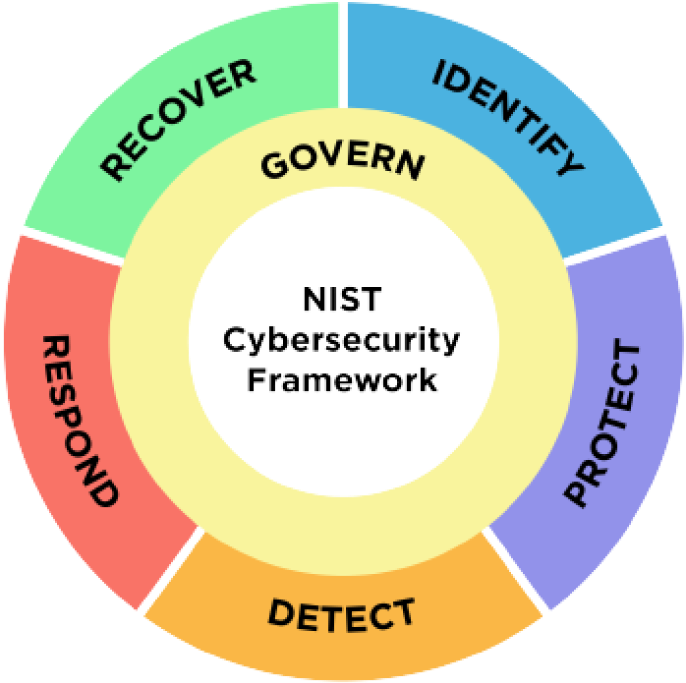
SmartVault’s information security policies and practices govern the management of security for SmartVault’s operations, and the services provided to its customers, and which apply to all SmartVault personnel, including employees, and contractors. These policies are aligned with the ISO/IEC 27001:2022 standard and guide security within SmartVault.
Documents
Data Security
Data Security
We follow industry best practices for data security. We are happy to provide more details about our data security practices upon request.
Data Privacy
Data Privacy
Privacy of customer data is top of mind. We follow industry best practices and follow all applicable privacy regulations.
Access Control
Access Control
Access is tightly monitored and controlled at our company. We are happy to provide more details about our access control practices upon request.
Infrastructure
Infrastructure
We take great care to work with best-in-class infrastructure providers that provide secure computing and storage. We are happy to provide more details about our infrastructure upon request.